SAML is a technology for user authentication, not user authorization, and this is a key distinction. User authorization is a separate area of identity and access management. Authentication refers to a user's identity: who they are and whether their identity has been confirmed by a login process.
Does SAML provide authorization?
SAML does not do authorization explicitly. It simply provides the attributes in the SAML token and it's up to the application as to how these are handled.Is SAML basic authentication?
The sample application in Spring SAML contains both basic authentication with username and password and SAML-based authentication but the Basic Auth portion uses local accounts defined in the securityContext.What is SAML authorization?
A Security Assertion Markup Language (SAML) authorization assertion contains proof that a certain user has been authorized to access a specified resource. Typically, such assertions are issued by a SAML Policy Decision Point (PDP) when a client requests access to a specified resource.How SAML is being used?
SAML is primarily used to enable web browser single sign-on (SSO). The user experience objective for SSO is to allow a user to authenticate once and gain access to separately secured systems without resubmitting credentials.SAML 2.0: Technical Overview
What is the difference between SAML and OAuth?
SAML supports Single Sign-On while also supporting authorization by the Attribute Query route. OAuth is focused on authorization, even if it is frequently coerced into an authentication role, for example when using social login such as “sign in with a Facebook account”. Regardless, OAuth2 does not support SSO.Where is SAML used?
SAML - Most commonly used by businesses to allow their users to access services they pay for. Salesforce, Gmail, Box and Expensify are all examples of service providers an employee would gain access to after a SAML login. SAML asserts to the service provider who the user is; this is authentication.What protocol does SAML use?
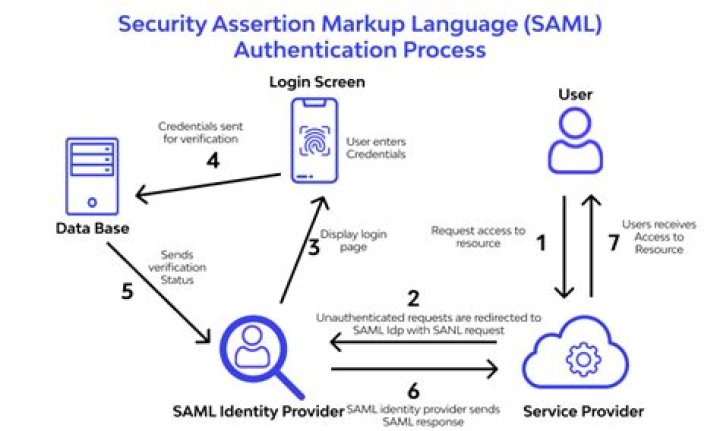
SAML 2.0 is an XML-based protocol that uses security tokens containing assertions to pass information about a principal (usually an end user) between a SAML authority, named an Identity Provider, and a SAML consumer, named a Service Provider.How does SAML work with SSO?
SAML SSO works by transferring the user's identity from one place (the identity provider) to another (the service provider). This is done through an exchange of digitally signed XML documents.What type of authentication is SAML?
SAML is an open standard used for authentication. Based upon the Extensible Markup Language (XML) format, web applications use SAML to transfer authentication data between two parties - the identity provider (IdP) and the service provider (SP).Can SAML and OAuth work together?
Can you use both SAML and OAuth? Yes, you can. The Client can get a SAML assertion from the IdP and request the Authorization Server to grant access to the Resource Server. The Authorization Server can then verify the identity of the user and pass back an OAuth token in the HTTP header to access the protected resource.What is the difference between SAML and Kerberos?
Kerberos is a lan (enterprise) technology while SAML is Internet. Kerberos requires that the system that requests the ticket (asks for user identity, in a way )is also in the kerberos domain, SAML does not require systems to sign up before.What SAML response contains?
A SAML Response is sent by the Identity Provider to the Service Provider and if the user succeeded in the authentication process, it contains the Assertion with the NameID / attributes of the user. There are 8 examples: An unsigned SAML Response with an unsigned Assertion.Does SAML use LDAP?
SAML itself doesn't perform the authentication but rather communicates the assertion data. It works in conjunction with LDAP, Active Directory, or another authentication authority, facilitating the link between access authorization and LDAP authentication.How do you implement SAML?
Implementation of SAML SSO follows 5 simple steps which are outlined in detail below.
- Step 1: Exchange of metadata information. ...
- Step 2: Identity provider configuration. ...
- Step 3: Enable SAML in Configuration. ...
- Step 4: Test the single sign-on connection. ...
- Step 5: Go live.
Why do we need SAML?
SAML simplifies federated authentication and authorization processes for users, Identity providers, and service providers. SAML provides a solution to allow your identity provider and service providers to exist separately from each other, which centralizes user management and provides access to SaaS solutions.Is SAML MFA?
MFA using SAML configurationSAML can also be used to configure MFA between different devices. In an enterprise where we have different SPs used by multiple hosts. By using SAML we can enforce MFA in any of the below ways.